One of the goals of taking over the router is to get control of the Domain NameSystem on the router, so an attacker can reroute traffic of certain sites to hisown site (a so called 'man in the middle' attack). There are a few possible wayshow this could be done, where UPnP can be used as part of the hack. Please notethat the methods described here are possible ways to get access to DNS, but Ihave not actually got them to work, or have not found the time to work on it,like in the case of making a customized firmware.
- Hack Router Port 53 Tcp Ip
- Hack Router Port 53 Tcp Number
- Hack Port 53
- Hack Router Port 53 Tcp Code
- Hack Router Port 53 Tcp Login
Hack Router Port 53 Tcp Ip
DNS has always been designed to use both UDP and TCP port 53 from the start 1, with UDP being the default, and fall back to using TCP when it is unable to communicate on UDP, typically when the packet size is too large to push through in a single UDP packet. When Does DNS Switch to TCP? Many routers allow port 53 (UDP and TCP) on the WAN port the router to be portmapped to port 53 (UDP and TCP) on the inside of the router itself, exposing the DNS on the router to the outside world. The DNS servers on most routers seem to be pure forwarders though, with no caching. Uploading new firmware. TCP/UDP port 53, showing that a DNS server is running. TCP ports 80, 443, and 8080. Sep 8, 2015 - Too many DNS servers enable bad actors to hijack them for DDoS attacks. An attacker could connect using the email server's email SMTP receiving port (TCP port 25) and send. Devices (such as wireless routers) running unexpected DNS servers. Security Data Security.
- Well both of the hacking has the same process. Let’s summarize what we must do. Confirm the website or a computer you want to hack. Find or trace their IP address. Make sure that IP address is online Scan for open ports Check for vulnerable ports ( enumerate the services running on ports and try.
- Me bei impatient, I wanted to check if my Kali Linux was actually doing anything to ADSL router hack. I used following command in a separate Terminal to monitor what my PC was doing it was doing a lot tcpdump -ni eth0 That’s a lot of connected hosts with TCP Port 80 open. Some got ‘tcpwrapped’ marked on them.
Accessing DNS from the outside
Many routers allow port 53 (UDP and TCP) on the WAN port the router to beportmapped to port 53 (UDP and TCP) on the inside of the router itself,exposing the DNS on the router to the outside world. The DNS servers on mostrouters seem to be pure forwarders though, with no caching.
Uploading new firmware
While not directly because of UPnP, but if you can get the adminstrativeinterface access on the outside with a UPnP port forward and the defaultpassword is still on, you could upload a new firmware, that is nearly exactlythe same, except for DNS.
To properly recreate a firmware you need tohave good knowledge about how the firmware on the device is constructed,compile a few new executables, use the right offsets in the firmware and hopethat the device will accept it and it will not be bricked and no one detectsthat the device has been tampered with. For crackers this is currently tooexpensive to do, but it is certainly the most effective way.
Asynchronous digital subscriber line (DSL or ADSL) modem is a device used to connect a computer or router to a telephone line which provides the digital subscriber line service for connectivity to the Internet, which is often called DSL or ADSL broadband. In this guide I will show you show you how to scan IP range for connected ADSL or DSL modem routers and find DSL ADSL router hack remotely. This guide applies to Windows, Linux or Mac, so it doesn’t matter what’s your Operating system is, you can try the same steps from all these operating systems. The term DSL or ADSL modem is technically used to describe a modem which connects to a single computer, through a USB port or is installed in a computer PCI slot. The more common DSL or ADSL router which combines the function of a DSL or ADSL modem and a home router, is a standalone device which can be connected to multiple computers through multiple Ethernet ports or an integral wireless access point. Also called a residential gateway, a DSL or ADSL router usually manages the connection and sharing of the DSL or ADSL service in a home or small office network.
Put this together with Wireshark hacking for http websites, you got a nightmare for the user behind that router as all their passwords and details can be tracked very easily.
Installing NMAP
Hack Router Port 53 Tcp Number
I use Kali Linux which comes with NMAP Preinstalled. If you are using Windows or Mac (or any other flavour of Linux) go to the following website to download and install NMAP.
Linux Installation:
For Ubuntu, Debian or aptitude based system NMAP is usually made available via default repository. Install NMAP using the following command:
For YUM Based systems such as Redhat, CentOS, install via
For PACMAN based systems such as Arch Linux, install via
Windows Installation:
For Windows Computers, download installer and run the executable. Link: http://nmap.org/dist/nmap-6.46-setup.exe
Mac Installation:
For Mac users, download installer and install Link: http://nmap.org/dist/nmap-6.46.dmg
Hack Port 53
Official NMAP site
You can read more about NMAP here: http://nmap.org/
Search for Vulnerable Routers
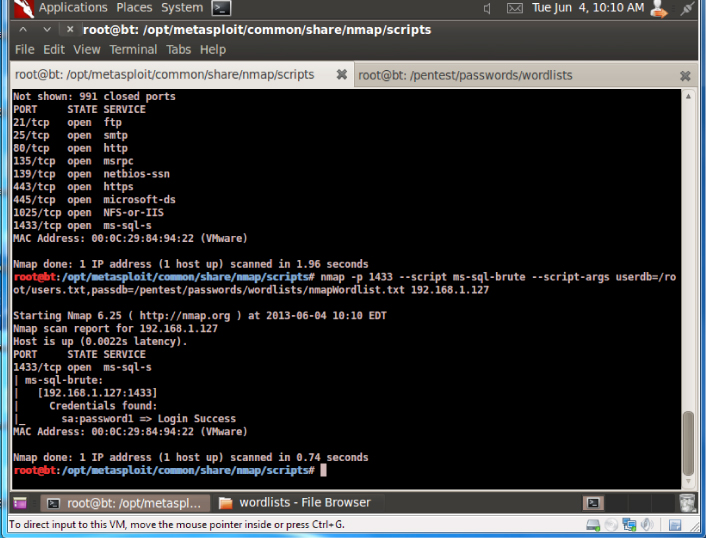
Now that we have NMAP sorted, we are going to run the following command to scan for ADSL Modem Routers based on their Banner on Port 80 to start our ADSL router hack. All you need is to pick an IP range. I’ve used an example below using 101.53.64.1/24 range.
Search from Linux using command Line
In Linux run the following command:
In Windows or Mac open NMAP and copy paste this line:
Once it finds the results, search for the word ‘open’ to narrow down results. A typical Linux NMAP command would return outputs line below: (and of course I’ve changed the IP details)
This was taking a long time (we are after all try to scan 256 hosts using the command above). Me being just impatient, I wanted to check if my Kali Linux was actually doing anything to ADSL router hack. I used the following command in a separate Terminal to monitor what my PC was doing… it was doing a lot …
That’s a lot of connected hosts with TCP Port 80 open. Some got ‘tcpwrapped’ marked on them. It means they are possibly not accessible.
Search from Windows, Mac or Linux using GUI – NMAP or Zenmap
Assuming you got NMAP installation sorted, you can now open NMAP (In Kali Linux or similar Linux distro, you can use Zenmap which is GUI version of NAMP cross platform). Copy paste the following line in Command field
another version of this command is using different representation of Subnet MASK.
Press SCAN Button and wait few minutes till the scan is over.
Once you have some results, then you need to find the open devices with open ports. In search Result page:
- Click on Services Button
- Click on http Service
- Click on Ports/Hosts TAB (Twice to sort them by status)
Hack Router Port 53 Tcp Code
As you can see, I’ve found a few devices with open http port 80.
It is quite amazing how many devices got ports open facing outer DMZ.
Access Management Webpage
Hack Router Port 53 Tcp Login
Pick one at a time. For example try this:
You get the idea. If it opens a webpage asking for username and password, try one of the following combinations:
If you can find the Router’s model number and make, you can find exact username and password from this webpage:http://portforward.com/default_username_password/ Before we finish up, I am sure you were already impatient like me as a lot of the routers had ‘tcpwrapped’ on them which was actually stopping us from accessing the web management interface to ADSL router hack. Following command will exclude those devices from our search. I’ve also expanded my search to a broader range using a slightly different Subnet MASK.
In this command I am using /22 Subnet Mask with 2 specific outputs: I am looking for the work ‘open’ and excluding ‘tcpwrapped’ on my output. As you can see, I still get a lot of outputs.
Conclusion
You’ll be surprised how many have default username and passwords enabled. Once you get your access to the router, you can do a lot more, like DNS hijacking, steal username and passwords (for example: Social Media username passwords (FaceBook, Twitter, WebMail etc.)) using tcpdump/snoop on router’s interface and many more using ADSL router hack … who didn’t change their routers default password, let them know of the risks.
But I am not here to judge whether it should be done or not, but this is definitely a way to gain access to a router. So hacking is not always bad, it sometime is required when you loose access or a system just wouldn’t respond. As a pentester, you should raise awareness. Share this guide as anyone who uses a Linux, Windows, Mac can use this guide to test their own network and fix ADSL router hack issue.
(‘-‘)/